policy settings
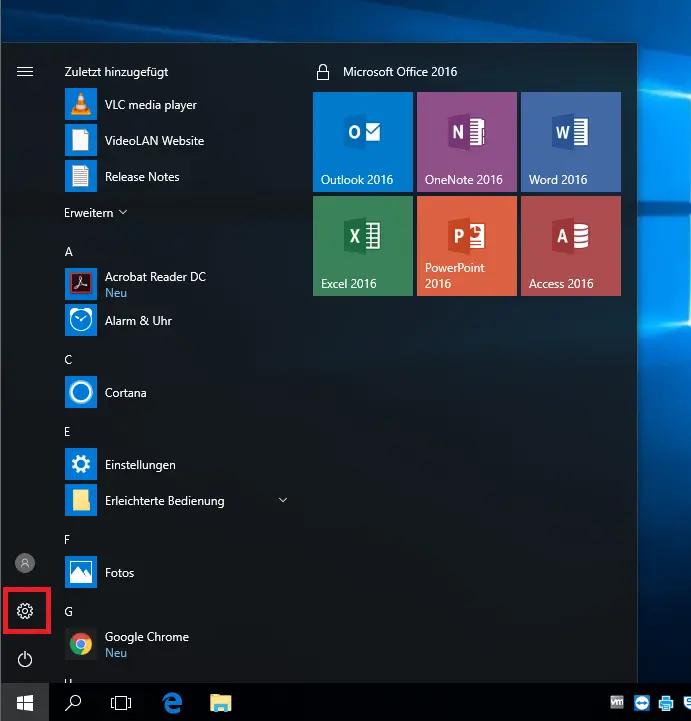
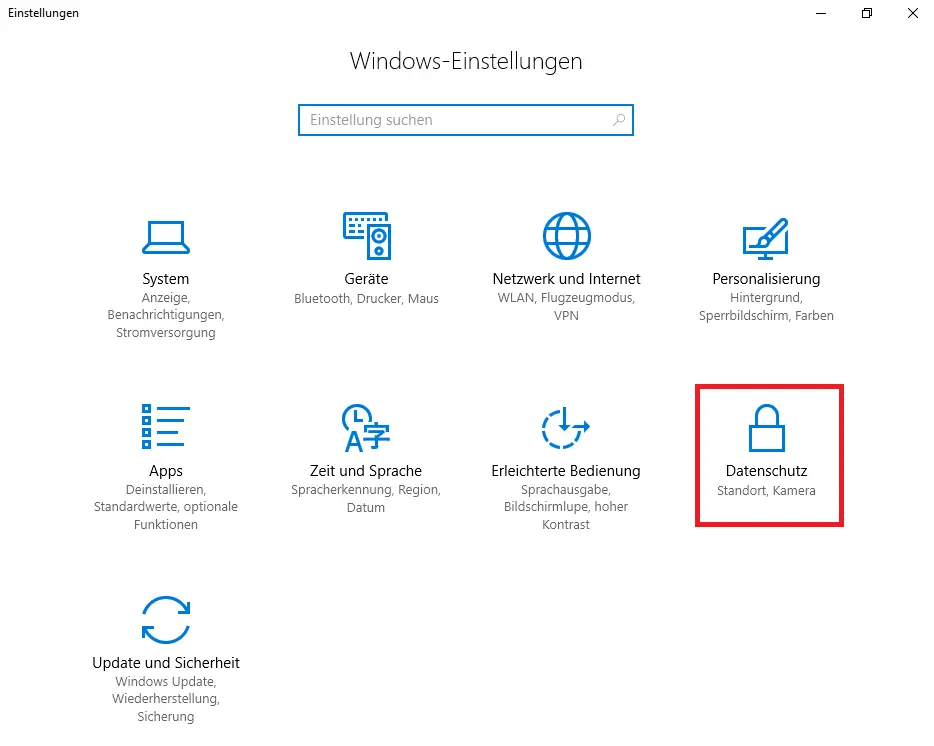
In the Windows settings ( image 1), you will find, among other things, the section "Data protection" ( image 2).
Microsoft Store Apps can usually send data to the cloud. The functions within the privacy settings mostly refer to the use of Microsoft Store Apps. Conventional software (desktop apps) such as Office are not affected by these. It should be noted that Edge, the calculator, photos and Skype are apps that are already included in Windows 10.
In general, the Microsoft privacy policy applies to everything about data privacy in Microsoft products, which is also linked and accessible in many places in Windows and the Microsoft apps.
All users are responsible for their own personal data and its use in Windows and other software. However, data from third parties may never be stored or processed without their knowledge and explicit approval..
A part of the privacy policy sections has already been preconfigured or isn't relevant in our environment and therefore no longer visible here.
For the remaining categories, it is not useful to restrict them already. Depending on the installed software and the individual use case, the user has to decide for himself which rights are to be granted to the specific programm or Windows. Every application that requires corresponding rights asks for the permission of the user. Examples are the use of the camera and the microphone when using Skype or the position data when using a map or navigation application.
There are explanations in the individual areas of what is behind the permissions, if necessary with links to further explanations or documentation.
BitLocker encryption of computers
The computer hard drives in all devices at the University of Erfurt are encrypted with BitLocker BitLocker encryption is a component of Windows 10. The encryption provides better protection for data in the case of theft. Users will not notice any noticeable effects of the encryption in normal everyday work.
In addition, BitLocker To Go encryption should be used to protect data on removable media such as USB sticks (see below).
The encryption of existing devices is not planned. If you would like this for your device, please contact the URMZ. In this case, however, assume that your device will have to be re-imaged and that your data will be lost in the process.
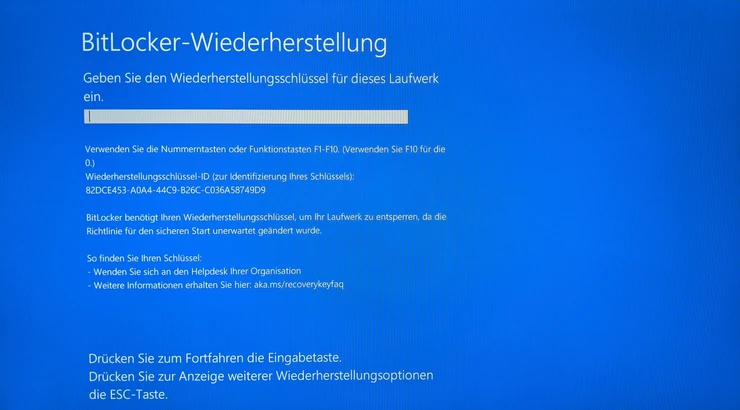
Under certain conditions (hardware changes, updates of special system components or malware), it may happen in rare exceptional cases that you are asked to enter a recovery key. You will then see the BitLocker recovery screen as shown in the picture.
In this case, please report to the URMZ. If it is not possible for the affected device to be unlocked by a member of the URMZ staff on site (e.g. stay in another place or even another country), the identity of the caller must be verified before the recovery key can be transmitted. Depending on the reason for the recovery, it may be necessary to re-image the device when it is back on campus.
When travelling abroad on business, please note that some countries have special regulations regarding the encryption of electronic devices and data carriers. Please enquire about the individual entry regulations of the respective country before travelling.
Encrypt USB sticks or memory cards (BitLocker To Go)
Should personal or other sensitive data need to be stored on USB sticks or memory cards, these must be encrypted and provided with a password.
According to the IT security policy of the University of Erfurt, the storage of data on removable media is only permitted in exceptional cases. The specifications of the IT security guideline, in particular under point 5.10 Data backup, must be observed.
Microsoft offers BitLocker drive encryption for encryption in Windows (Pro and Enterprise versions only).
Encryption
-
Connecting the USB stick or memory card
-
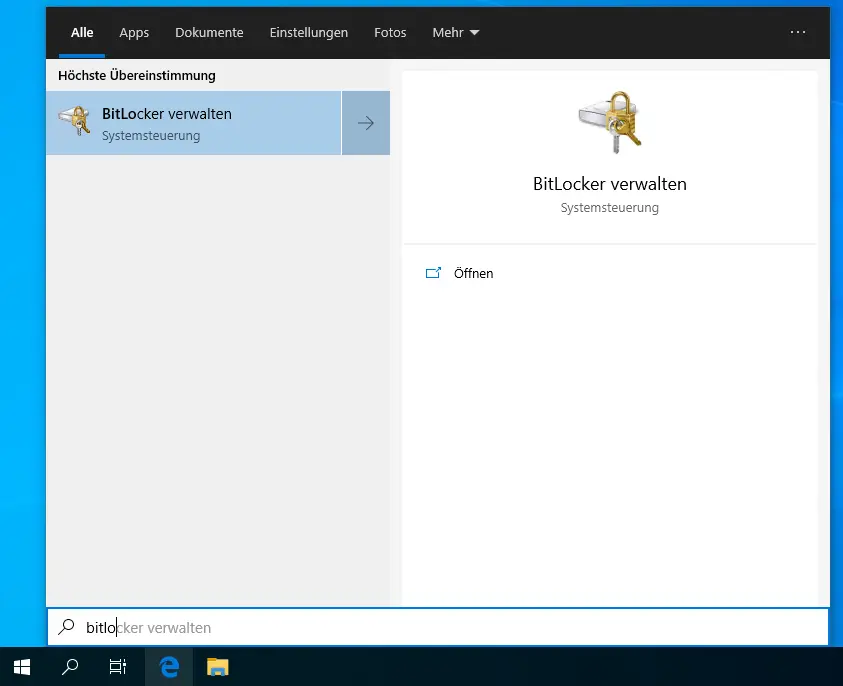
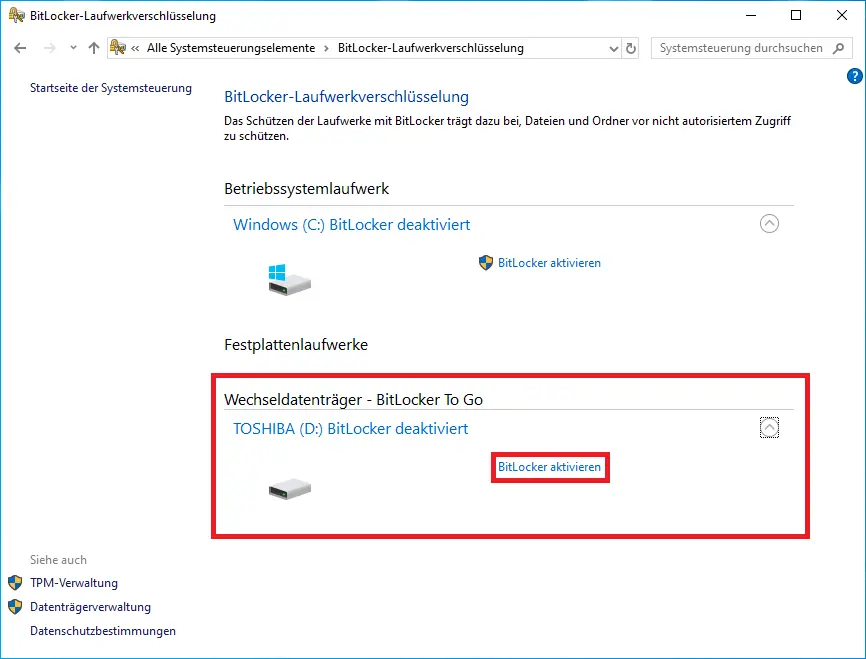
Enter "Bitlocker" in the Windows search and call up "Manage BitLocker" (image 1).
-
Select the stick or memory card to be encrypted under "Removable media - BitLocker To Go" (image 2).
-
Click on "Activate BitLocker" (image 2)
-
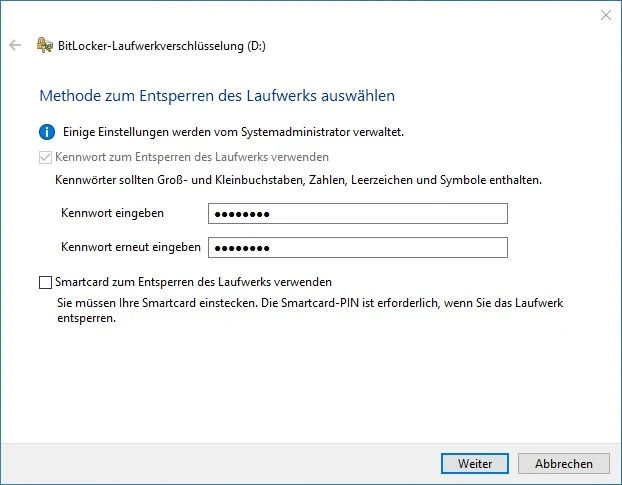
Assign a secure password with at least eight characters (image 3)
-
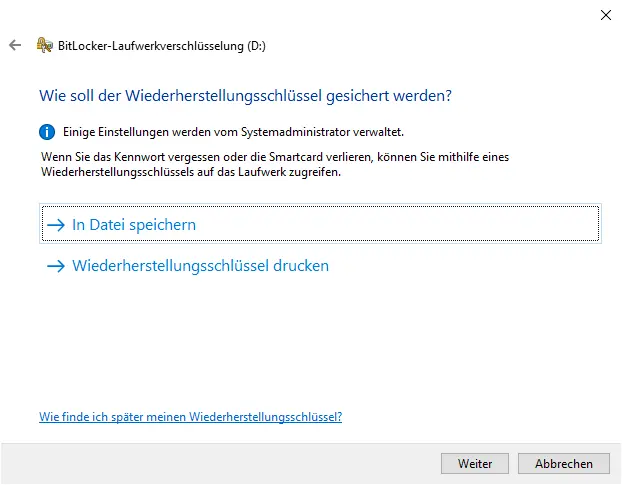
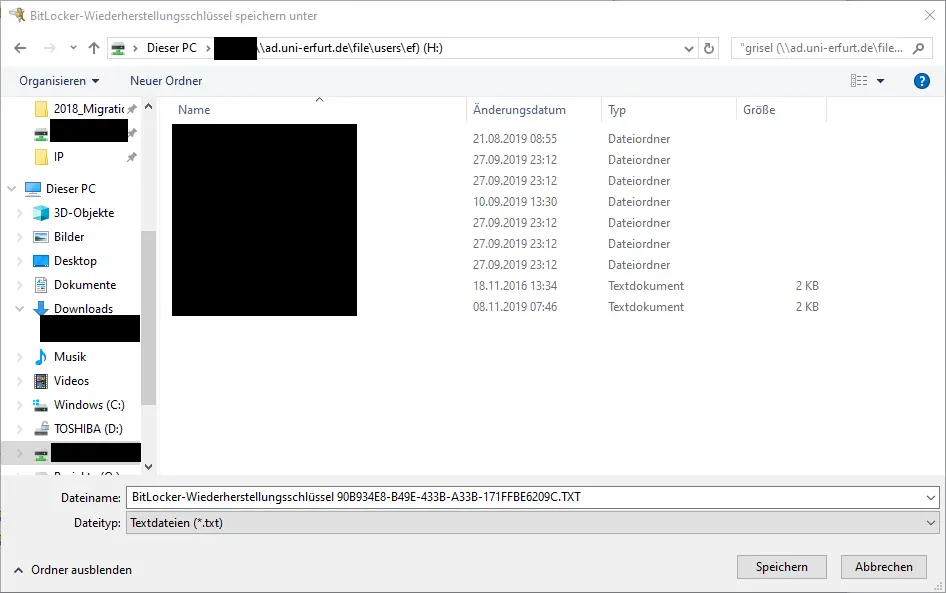
In the next step, select where the recovery key is to be saved. Select "Save to file" and store the file in several locations that only you can access, if possible at any time (e.g. in your home directory (H:) in connection with eduVPN for access from outside). (image4, 5)
-
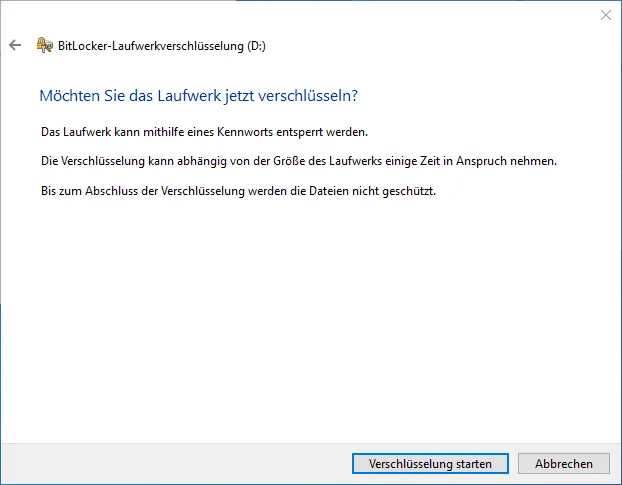
Click on "Start encryption" (image 6)
-
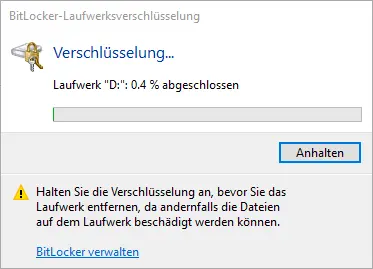
The drive will be encrypted (image 7) and finally a completion message will be displayed (image 8).
Never disconnect the USB stick or memory card from the computer during encryption. This can lead to data loss.
Decryption
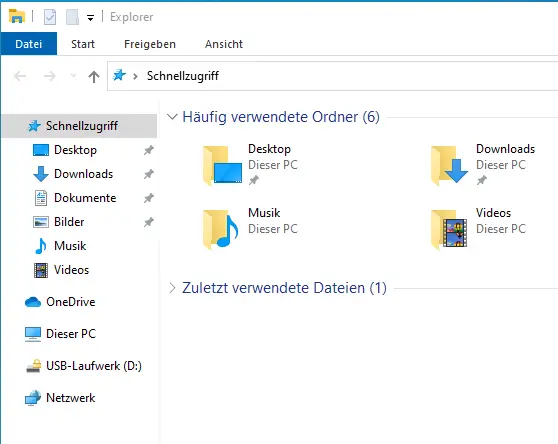
- Plug the device into another Windows PC. The removable disk appears in Windows Explorer with a lock on it. (Image 1)
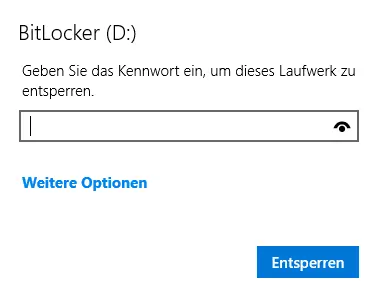
- When you select the BitLocker To Go encrypted drive, you will be asked for a password. Enter the password and click on "Unlock". Do NOT enter the recovery key at this point. ( Image 2)
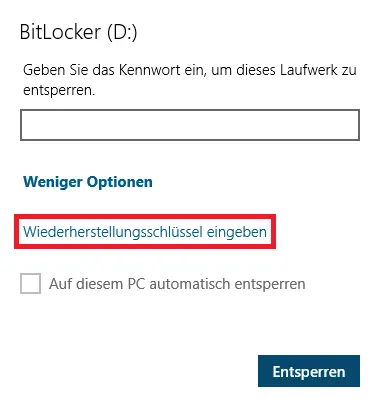
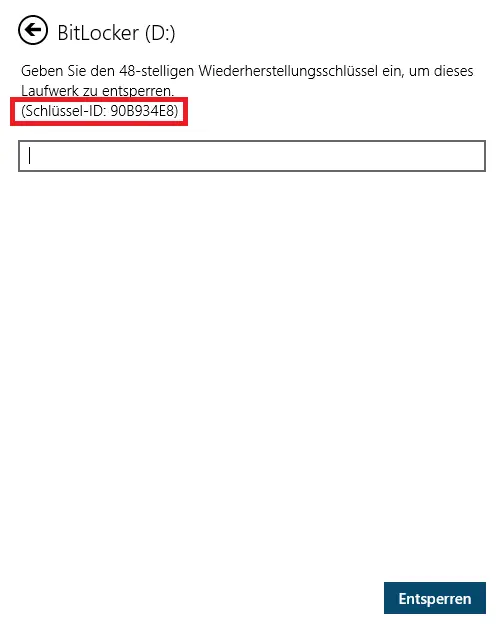
If you have forgotten the password, you can enter the recovery key at step 2 under "More options" (Image 3). To identify the unit and the associated key file or key, the first eight characters of the identifier are displayed (Image 4).
There are various programmes for accessing a BitLocker encrypted removable disk under MacOS and Linux, such as:
- https://www.m3datarecovery.com/mac-bitlocker/bitlocker-to-go-mac-download.html
- https://www.easyuefi.com/bitlocker-for-mac/resource/free-open-bitlocker-encrypted-drive-on-mac.html
If the flash drive or memory card is to be used for exchanging data with other people, never pass on the password together with the data medium. If possible, transmit the password directly to the other person. If this is not possible, then alternatively by telephone or e-mail.
When travelling abroad on business, please note that some countries have special regulations regarding the encryption of electronic devices and data carriers. Please enquire about the individual entry regulations of the respective country before travelling.
![[Translate to English:] Abschluss BitLocker-Verschlüsselung](/fileadmin/_processed_/b/8/csm_Bitlocker-To-Go-10_1d276b2bde.webp)